IT Services & Cybersecurity Tweaks that Benefit Nonprofits
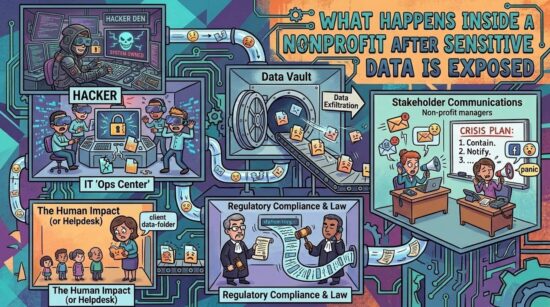
Donor management systems are the backbone of modern fundraising, but they’re also one of the most overlooked cybersecurity risks in the nonprofit sector. From shared logins to unsafe third-party integrations, many organizations unknowingly expose sensitive donor data every day. And with cyberattacks against nonprofits rising sharply, these hidden vulnerabilities can quickly turn into costly breaches.
In this deep dive, we’ll uncover the most common (and dangerous) security gaps inside donor management systems, and how nonprofits can begin addressing them.
Why Donor Management Systems Are Prime Targets
Nonprofits store highly valuable data:
-
Donor names, addresses, and emails
-
Payment details and transaction histories
-
Giving patterns and financial insights
This makes them extremely attractive to attackers. In fact, cybercriminals specifically target nonprofits because they often have valuable data but limited security resources.
The stakes are high:
-
Financial loss from fraud or downtime
-
Compliance risks for Legal firms
-
Long-term damage to donor trust
Learn how organizations mitigate these risks through our nonprofit IT consulting.
Excessive Access: When Too Many People Have Too Much Control
One of the most common (and dangerous) issues in donor systems is over-permissioned access.
The problem:
-
Staff, volunteers, and contractors all have broad system access
-
Permissions are rarely reviewed or revoked
-
Sensitive data is accessible to users who don’t need it
This creates ideal conditions for insider threats, which can be accidental or intentional.
Why it matters:
Even a single compromised account can expose your entire donor database.
Best practice:
-
Role-based access control (RBAC)
-
Regular permission audits
-
Least-privilege policies
For nonprofits lacking internal expertise, solutions like our award-winning it solutions can help implement proper access controls.
Shared Logins: A Silent but Serious Threat
Shared credentials are still surprisingly common in nonprofit environments. This is a top priority fix that with the right cybersecurity solutions.
The risks:
-
No accountability for user actions
-
Increased likelihood of password leaks
-
Easier entry point for attackers
Many breaches occur due to weak or shared credentials combined with lack of authentication controls.
Real-world impact:
If one shared password is compromised, attackers can:
-
Access donor records
-
Modify payment details
-
Launch phishing campaigns using your system
Best practice:
-
Unique logins for every user
-
Multi-factor authentication (MFA)
-
Password management policies
Unsafe Third-Party Integrations: The Hidden Backdoor
Modern donor systems rely heavily on integrations that benefit greatly from data protection.
-
Payment processors
-
Email marketing platforms
-
Event and fundraising tools
But every integration is a potential vulnerability.
The issue:
Nonprofits often trust vendors without fully vetting their security.
If a third-party system is breached, your donor data may be exposed—even if your internal systems are secure.
Common risks:
-
API vulnerabilities
-
Weak encryption standards
-
Data sharing without strict controls
Best practice:
-
Vendor security assessments
-
Limit data sharing between systems
-
Monitor integrations continuously
Lack of Visibility: You Can’t Protect What You Can’t See
Many nonprofits don’t have full visibility into:
-
Who is accessing donor data
-
When data is being exported
-
Where sensitive information is stored
This lack of monitoring allows threats to go undetected. In some cases, organizations don’t discover breaches until weeks or months later, increasing damage and recovery costs. Our managed IT services are designed to proactively monitor and identify these sort of threats.
Why this happens:
-
No centralized logging
-
Limited IT oversight
-
Outdated systems
Best practice:
-
Real-time monitoring and alerts
-
Audit logs for all system activity
-
Regular security assessments
Outdated Systems & Poor Security Hygiene
Many donor platforms suffer from:
-
Unpatched software
-
Legacy systems
-
Weak encryption
These issues create easy entry points for attackers.
Nonprofits often delay upgrades due to budget constraints, but outdated systems are one of the leading causes of breaches.
Additional risks:
-
Credential stuffing attacks
-
Malware infections
-
Ransomware targeting donor databases
Cyberattacks against nonprofits have surged significantly in recent years, with thousands of attacks occurring weekly across the sector.
Best practice:
-
Regular patching and updates
-
Endpoint security
-
Backup and recovery planning
Building a More Secure Donor Management Environment
While the risks are serious, they are also preventable.
A secure donor system includes:
-
Strong access controls
-
Unique user authentication
-
Secure integrations
-
Continuous monitoring
-
Regular security audits
Nonprofits that take a proactive approach not only reduce risk, they also strengthen donor trust.
Final Thoughts: Security Is a Trust Strategy
Cybersecurity isn’t just an IT issue, it’s a donor trust issue.
When supporters give to your organization, they trust you with their personal and financial information. A single breach can undo years of relationship-building.
By addressing hidden risks in donor management systems, nonprofits can:
-
Protect sensitive data
-
Ensure uninterrupted fundraising
-
Build long-term credibility with donors